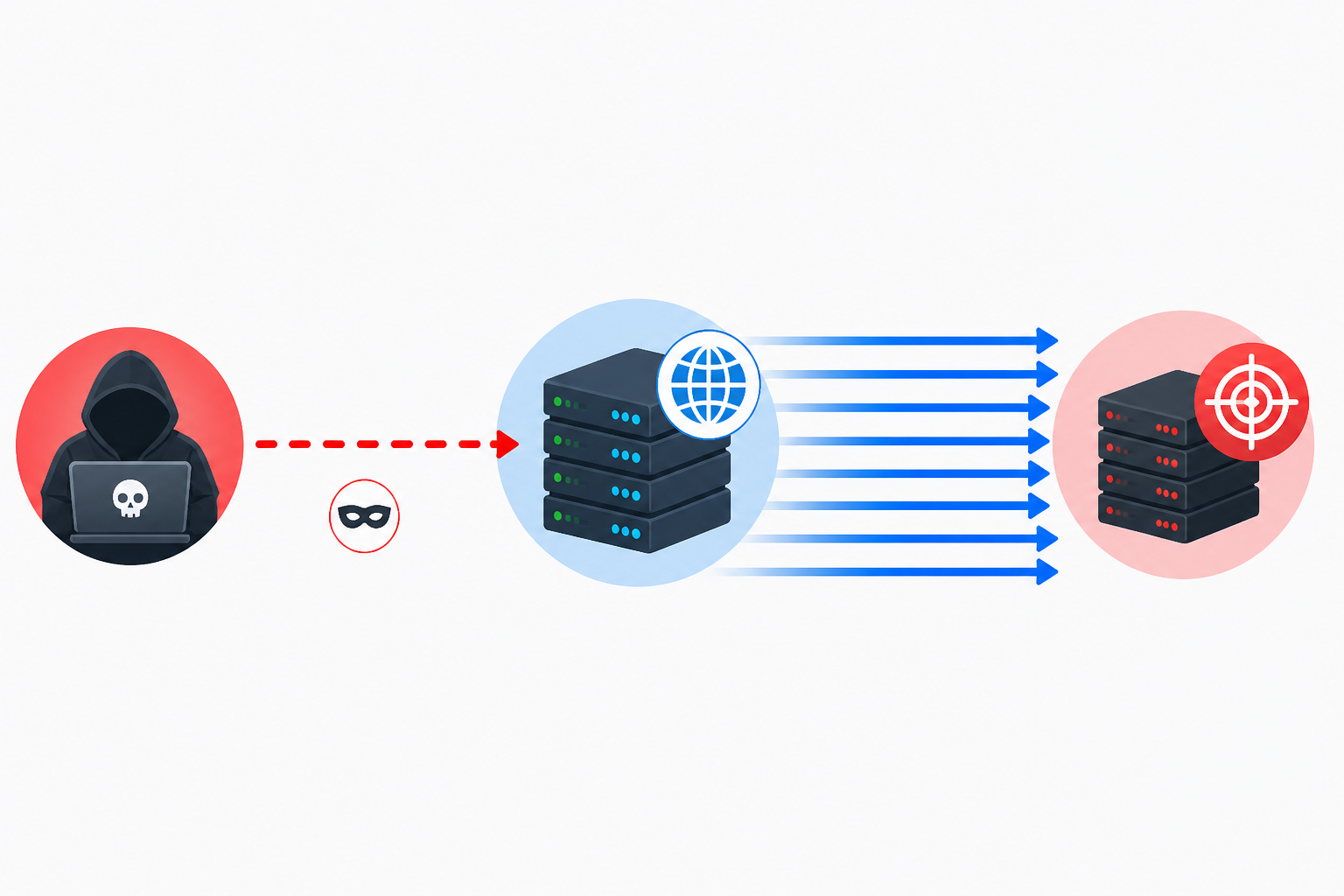
DNS Amplification attacks are a method commonly used in DDoS attacks that arise due to misconfiguration of the DNS protocol. Attackers exploit DNS servers as “amplifiers” to generate significantly larger traffic directed toward target systems.
This type of attack typically exploits two main vulnerabilities:
- UDP protocol does not perform validation
- Open DNS resolvers
How the attack works:
- The attacker sends a small DNS query
- The source IP is spoofed to the target system’s IP (IP spoofing)
- The DNS server generates a large response
- This response is sent to the target system
As a result:
- Small request → large response
- Traffic amplification can reach 50x – 100x levels
- The target system becomes overloaded and service becomes unavailable
Misconfigured DNS servers:
- Are used as “bots” in DDoS attacks
- Can cause IP addresses to be blacklisted
- Consume server resources (CPU / RAM / Network)
- May lead to access restrictions by hosting providers
The most critical rule for DNS servers:
Public DNS servers should not act as recursive resolvers.
They should only operate in the following role:
- Authoritative DNS (authoritative name server)
To prevent DNS amplification attacks, the following configurations should be applied:
recursion no;
allow-recursion { none; };
or, for local usage only:
allow-recursion { 127.0.0.1; localhost; };
Plesk Server Security Configuration
Plesk runs the BIND (named) service in a chroot environment and automatically generates configuration files.
In Plesk environments:
- named.conf should not be edited directly
- Settings should be applied via override files or the control panel
Step 1: Disable DNS recursion via panel
In Plesk:
Tools & Settings → DNS Server Settings
Set:
- Recursion → Disabled or Localnets
Step 2: Using an override file
/etc/named-user-options.conf
Inside the file:
recursion no;
Step 3: Restart the service
Plesk uses chroot:
systemctl restart named-chroot.service
You can verify the configuration with:
named-checkconf
Test:
dig @127.0.0.1 google.com
If recursion is disabled, the response should either not be returned or show REFUSED.
cPanel Server Security Configuration
cPanel typically uses BIND (named).
In /etc/named.conf:
options {
recursion no;
allow-recursion { none; };
};
After applying the changes, restart the service:
systemctl restart named
Leave a Comment
* Your comment will be published after approval.




Comments
0No comments yet. Be the first to comment!